Course description
Course Title: Cyber Security Architecture
The Cyber Security Architecture course is a
comprehensive, hands-on program designed to equip learners with the knowledge
and practical skills required to design, assess, and implement secure
enterprise architectures. This course goes beyond theory to provide real-world
architectural design approaches aligned with globally recognized frameworks
such as National Institute of Standards and Technology (NIST), International
Organization for Standardization (ISO/IEC 27001), and The Open Group (TOGAF).
Participants will learn how to build layered security
architectures that protect networks, endpoints, applications, cloud platforms,
identities, and data assets. The course integrates risk-based security design
principles, Zero Trust concepts, defense-in-depth strategies, secure
segmentation models, and secure cloud adoption frameworks to prepare
professionals for modern hybrid enterprise environments.
The program is structured to simulate the real
responsibilities of a Security Architect — including translating business
requirements into secure designs, creating architectural diagrams (HLDs &
LLDs), defining security controls, and aligning security strategy with
governance and compliance mandates.
Module 1: Foundations of Cyber Security Architecture
- Principles
of security architecture
- CIA
triad and security design models
- Risk
management integration into architecture
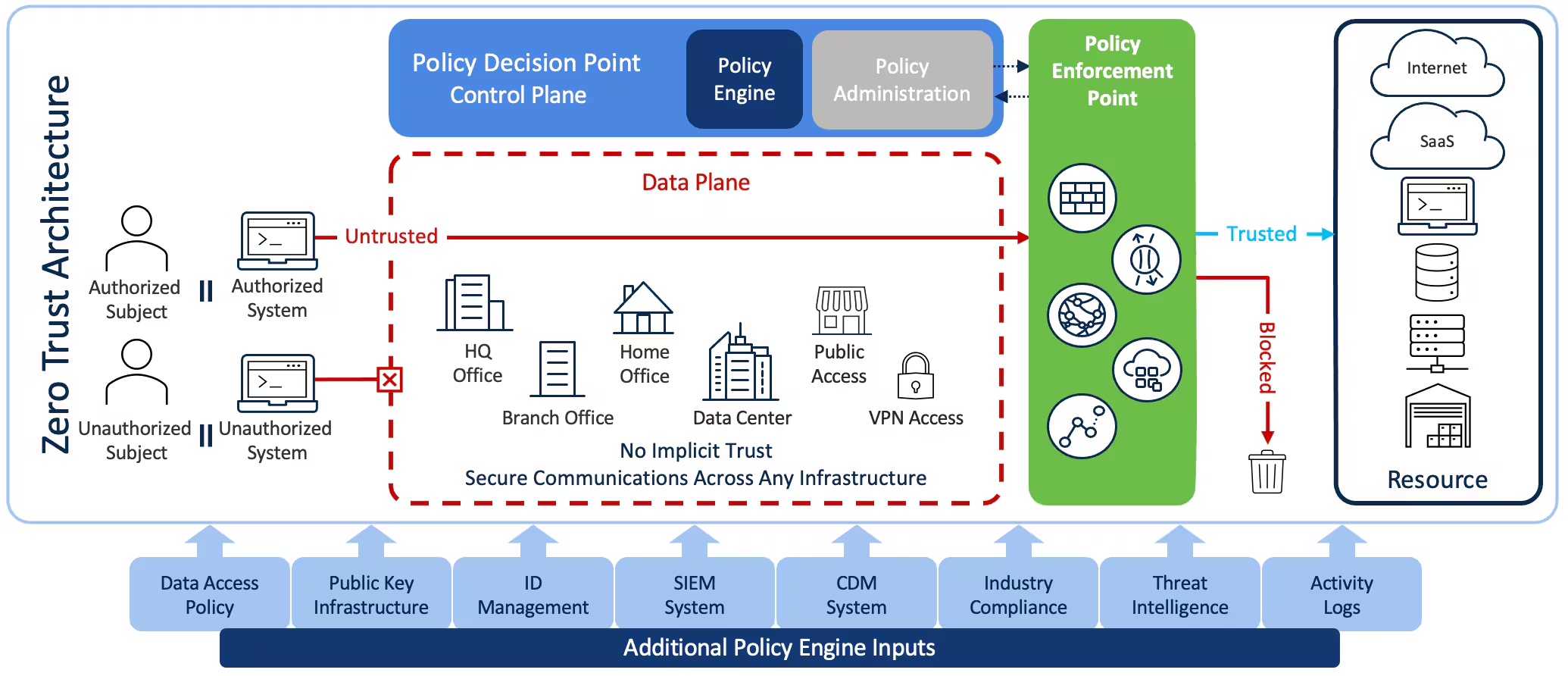
- Defense-in-depth
and Zero Trust Architecture
Module 2: Enterprise Security Architecture Frameworks
- NIST
Cybersecurity Framework (CSF)
- ISO/IEC
27001 architectural alignment
- TOGAF
and SABSA security architecture methodology
- Governance,
Risk & Compliance (GRC) integration
Module 3: Network Security Architecture
- Secure
network segmentation and micro-segmentation
- Firewall
architecture and rule design
- DMZ,
reverse proxy, VPN, and secure remote access design
- Secure
SD-WAN and branch architecture
- IDS/IPS
and NDR placement strategies
Module 4: Identity & Access Security Architecture
- Identity
lifecycle management
- Privileged
Access Management (PAM) architecture
- Multi-Factor
Authentication (MFA) design
- Zero
Trust access control models
- Integration
with Active Directory & cloud identity providers
Module 5: Cloud Security Architecture
- Secure
AWS, Azure, and hybrid cloud design
- Cloud
shared responsibility model
- Secure
workload deployment patterns
- CASB,
CSPM, and container security architecture
- DevSecOps
integration
Module 6: Application & Data Security Architecture
- Secure
SDLC integration
- API
security architecture
- Encryption
and key management systems
- Data
classification and DLP architecture
- Database
Activity Monitoring (DAM) design
Module 7: Security Operations & Monitoring
Architecture
- SIEM
architecture design
- SOAR
integration models
- Log
management architecture
- Incident
response workflow design
- Threat
intelligence integration
Module 8: Architectural Documentation & Real-World
Design
- Creating
High-Level Designs (HLD)
- Developing
Low-Level Designs (LLD)
- Architecture
review board simulation
- Building
implementation roadmaps
- Cost
estimation and bill of materials (BOM) planning
Participants will receive:
- ✔ Complete
Cyber Security Architecture slide deck (professional training material)
- ✔ Architecture
design templates (HLD & LLD samples)
- ✔ Security
policy and control mapping templates
- ✔ Sample
enterprise security architecture diagrams
- ✔ Risk
assessment and control mapping workbook
- ✔ Real-world
case study exercises
- ✔ Capstone
project: Full enterprise security architecture design
- ✔ Certificate
of Course Completion
- ✔ Lifetime
access to course materials (for online learners)
By the end of this course, learners will be able to:
- Design
secure enterprise architectures aligned with global standards
- Develop
complete network, cloud, and identity security models
- Translate
business requirements into secure architectural blueprints
- Create
professional HLD and LLD security documentation
- Architect
Zero Trust and risk-based security environments
- Prepare
for Security Architect, Senior Security Engineer, and GRC leadership roles
This course is ideal for Security Engineers, Network
Architects, Cloud Engineers, SOC Analysts transitioning into architecture
roles, IT Managers, and cybersecurity professionals seeking to elevate their
design-level expertise.